EMV Caveats
While EMV is a significant step in the right direction in terms of credit card security, the standard is not intended to be a complete and immediate security solution to prevent ALL credit card fraud. Specifically, EMV’s intent is to curb counterfeit credit cards being used in card present (such as in stores) situations. However, other fraudulent credit card uses and exploits will remain largely unsolved for a while. This was apparent when Europe rolled out EMV. Namely, when it was initially implemented in France, the card-present fraud did drop by 35% (between 2004 – 2009), but the card-not-present fraud (such as fraud committed online) increased by 360%. Likewise, in many countries where magstripe cards were used as a fallback payment mechanism, criminals would simply continue to use counterfeit magstripe cards to make purchases.
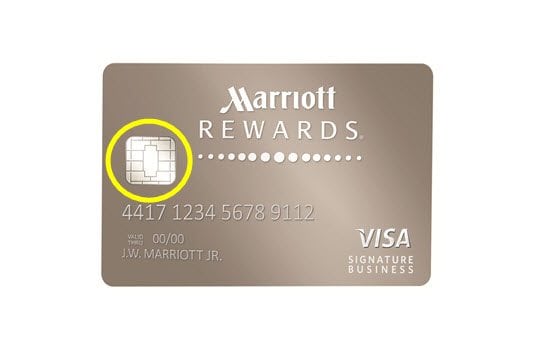
The fact that the specification is only designed to solve counterfeit credit card fraud is apparent when it comes to data security. The encryption used during the process is leveraged for credit card authentication, but not for data transmission [6]. The transmission of PAN (Primary Account Number) and other data can still occur in clear text. This makes it potentially vulnerable to interception by hackers. Security breaches such as the Target breach where credit card numbers were stolen by hackers could still potentially occur because merchants could still store and transmit data unencrypted [6]. These data could then be used to create counterfeit magstrip cards or leveraged fraudulently online.
To prevent this kind of fraud, the industry should implement encryption and tokenization. Encrypting credit card transactions would prevent hackers from stealing data while being transmitted or stored on a server. Moreover, tokenization would replace the actual card number with a token, which would essentially be useless to hackers even if they could get their hands on it. In fact, some technologies like ApplePay already do this while maintaining compatibility with the EMV Contactless specification [4]. According to Shift4, maker of a tokenization gateway, when EMV is implemented as part of a complete solution it can make a real difference in eliminating credit card fraud.
Another set of vulnerabilities relative to EMV centers around actual implementations. EMV is merely a specification, but every company that creates EMV technology must somehow implement it. The implementers typically do so properly, but there have been instances where software developers were simply careless or uninformed and unknowingly created security holes. One such example was when researchers in Europe discovered that random numbers used to insure that credit card transactions are unique and thus cannot be simply re-played were in fact not so random. These security experts were able to in effect “clone” a valid transaction and re-play it against an ATM to withdraw money [2]. This was not a flaw with issuers or payment network systems. It was not even a flaw within the card firmware. Instead, the flaw rested with the software leveraged by the ATM.
Similarly, and even more concerning are potential issues with contactless chip cards because the transmission of card information to a wireless reader is unencrypted. This transmission typically only works when the card is held 2-3 inches away from a reader, but there have been some reports that hackers can boost wireless signals up to 25 feet and essentially snag the card data remotely without the person ever knowing it. While the contactless cards typically do not include cardholder name, address, or the CVV, it’s plausible that hackers could use social engineering (or other means) to obtain its target’s name and address, and leverage them on e-commerce sites that do not require a CVV [8].
Regardless of any potential issues, most experts would agree that EMV is a step in the right direction. There is no doubt that the technology specification will continue to evolve, but at least the payment industry is moving forward. There will always be an ever-present cat-and-mouse game between the security establishment and criminals, but perhaps these latest technologies will tip the scales in the industry’s and thus in the consumers’ favor.
Vladimir Collak Vlad currently serves as president and CEO of Ignite Media. Ignite builds mobile and web solutions primarily for the Oil & Gas industry that includes clients such as Mansfield Oil, Enbridge, Total Safety, Universal Plant Services and others. Vladimir holds a BS degree in Information Technology and an MBA from the University of Texas at Tyler. He can be found on his blog at www.collak.net and at [email protected]
References
1. http://www.esecurityplanet.com/mobile-security/emv-is-no-payment-security-panacea.html
2. http://sec.cs.ucl.ac.uk/users/smurdoch/papers/oakland14chipandskim.pdf
3. https://www.emvco.com/about_emvco.aspx?id=202
4. http://support.verifone.com/fstore/0a463145bbfccb42_17e67747_1491c67f2a9_-6932/Apple%20Pay%20FAQ%20External.pdf
5. http://usa.visa.com/merchants/grow-your-business/payment-technologies/credit-card-chip/liability-shift.jsp
6. http://www.firstdata.com/downloads/thought-leadership/EMV-Encrypt-Tokenization-WP.PDF
7. http://blogs.wsj.com/cio/2015/04/29/broad-emv-adoption-for-plastic-cards-wont-happen-until-2020-forrester/
8. http://www.click2houston.com/news/thieves-easily-stealing-credit-card-info-by-electronic-pickpocketing/25026758